
Many people share online accounts, even in situations where high privacy and security are expected. As with everything in life, the sharing of these accounts does not endure forever. In a study conducted by my PhD students Borke Obada-Obieh and Yue Huang, we investigated the privacy and security challenges that people experience when they stop online account sharing.
Continue reading





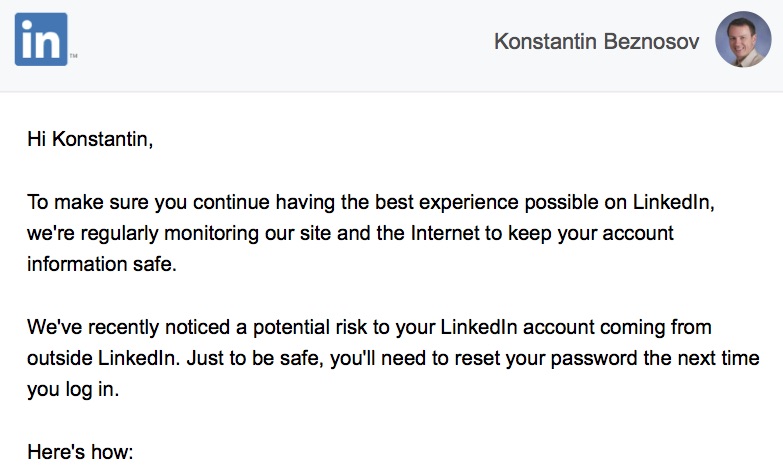
 This paper reports on a design and development of a mobile game prototype as an educational tool helping computer users to protect themselves against phishing attacks. The elements of a game design framework for avoiding phishing attacks were used to address the game design issues. Our mobile game design aimed to enhance the users’ avoidance behaviour through motivation to protect themselves against phishing threats.
This paper reports on a design and development of a mobile game prototype as an educational tool helping computer users to protect themselves against phishing attacks. The elements of a game design framework for avoiding phishing attacks were used to address the game design issues. Our mobile game design aimed to enhance the users’ avoidance behaviour through motivation to protect themselves against phishing threats. 