
Paper co-authored by my PhD students Yue Huang and Borke Obada-Obieh has received a Honourable Mention award at CHI 2020. Such awards are given to top 2-6% submissions.
Yue and Borke spoke to 26 Canadian adults who used shared smart speakers at home, including Amazon Echo, Google Home and Apple HomePod. We found that participants not only worried about keeping their data safe from the manufacturer or other entities; they also feared potential misuse of the device by people they actually live with and know.
Continue reading





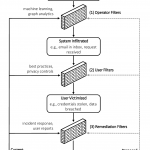 The orthodox paradigm to defend against automated social-engineering attacks in large-scale socio-technical systems is reactive and victim-agnostic. Defenses generally focus on identifying the attacks/attackers (e.g., phishing emails, social-bot infiltrations, malware offered for download). To change the status quo, we propose in
The orthodox paradigm to defend against automated social-engineering attacks in large-scale socio-technical systems is reactive and victim-agnostic. Defenses generally focus on identifying the attacks/attackers (e.g., phishing emails, social-bot infiltrations, malware offered for download). To change the status quo, we propose in 