With a remote workforce and everyone working digitally, the threat landscape increases. A team of my research group, led by PhD candidate Borke Obada-Obieh, performed the first qualitative study on employee security and privacy concerns when telecommuting.
Continue readingCategory Archives: IT security management
Improving Access Review with AuthzMap
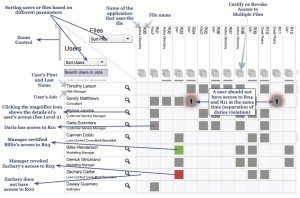 Research led by LERSSE Ph.D. student Pooya Jaferian will be featured at SOUPS this July. By interviewing IT professionals, he has explored access review activity in organizations, and then modeled access review in the activity theory framework. The model suggests that access review requires an understanding of the activity context including information about the users, their job, their access rights, and the history of access policy. Guidelines of the activity theory were used to design a new user interface, AuthzMap, which was compared to two state of the practice. The experiments demonstrated that AuthzMap improved the efficiency of access review most scenarios. Read the full paper for details.
Research led by LERSSE Ph.D. student Pooya Jaferian will be featured at SOUPS this July. By interviewing IT professionals, he has explored access review activity in organizations, and then modeled access review in the activity theory framework. The model suggests that access review requires an understanding of the activity context including information about the users, their job, their access rights, and the history of access policy. Guidelines of the activity theory were used to design a new user interface, AuthzMap, which was compared to two state of the practice. The experiments demonstrated that AuthzMap improved the efficiency of access review most scenarios. Read the full paper for details.
Project Presentations at Graduate Course in Security
Students in my graduate course on computer security are presenting their term papers on April 10. The topics vary from evaluation of Sybil detection mechanisms to detection of DDoS attacks on grid clusters. This mini-conference is open to public.
Heuristics for Evaluating IT Security Management Tools
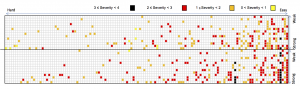 The usability of IT security management (ITSM) tools is hard to evaluate by regular methods, making heuristic evaluation attractive. However, standard usability heuristics (e.g., Nielsen’s) are hard to apply, as IT security management occurs within a complex and collaborative context that involves diverse stakeholders. In a joint project with CA Technologies, my Ph.D. student Pooya Jaferian has proposed a set of ITSM usability heuristics that are based on activity theory, are supported by prior research, and consider the complex and cooperative nature of security management. The paper reporting the evaluation of the heuristics received Best Paper Award at SOUPS ’11.
The usability of IT security management (ITSM) tools is hard to evaluate by regular methods, making heuristic evaluation attractive. However, standard usability heuristics (e.g., Nielsen’s) are hard to apply, as IT security management occurs within a complex and collaborative context that involves diverse stakeholders. In a joint project with CA Technologies, my Ph.D. student Pooya Jaferian has proposed a set of ITSM usability heuristics that are based on activity theory, are supported by prior research, and consider the complex and cooperative nature of security management. The paper reporting the evaluation of the heuristics received Best Paper Award at SOUPS ’11.
CHI Work in Progress to Feature LERSSE Research
This year, in Vancouver, Work In Progress Posters session of SIG CHI Conference will feature three research projects of my graduate students.

