 SOUPS ’16 paper on the prevalence of snooping on mobile phones has received Distinguished Paper award. The paper reports a series of quantitative studies that allowed a more accurate measurement of this phenomena. The study was led by our collaborators at the University of Lisbon. It was inspired by our previous study presented at Mobile CHI ’13. Continue reading
SOUPS ’16 paper on the prevalence of snooping on mobile phones has received Distinguished Paper award. The paper reports a series of quantitative studies that allowed a more accurate measurement of this phenomena. The study was led by our collaborators at the University of Lisbon. It was inspired by our previous study presented at Mobile CHI ’13. Continue reading
Category Archives: mobile security and privacy
Collaborative Study of Snooping on Mobile Phones Gets SOUPS Award
What I Love About My Research
As part of Innovate (in October) 2015, I gave a 7-minute “edutainment” talk, explaining in a very accessible form my current research, using an example of a recent study of iPhone’s TouchID:
Findings on Touch ID in plain (British) English
My research group had a paper presented at SOUPS on the interplay between TouchID and iPhone security, which I’ve described in a recent post. Here’s a video made by a wonderful team at Kindea Labs that explains the key findings in language accessible virtually to anyone:
Android Rooting: Methods, Detection, and Evasion
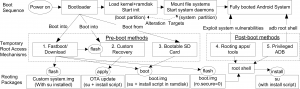 User root their Android (or jailbreak their iPhone) smartphones. They do so in order to run useful apps that require root privileges, to remove restrictions by carriers and hardware manufacturers, and to alter or remove system apps. Rooted devices are prevalent. According to a recent Android security report, Google Verify Apps detected rooting apps installed on approximately 2.5M devices.
User root their Android (or jailbreak their iPhone) smartphones. They do so in order to run useful apps that require root privileges, to remove restrictions by carriers and hardware manufacturers, and to alter or remove system apps. Rooted devices are prevalent. According to a recent Android security report, Google Verify Apps detected rooting apps installed on approximately 2.5M devices.
Touch ID: How Does It Affect iPhone Security?
 Recently, Apple has introduced Touch ID, which allows a fingerprint-based authentication to be used for iPhone unlocking. It’s positioned to allow users to use stronger passcodes for locking their iOS devices, without substantially sacrificing usability. It is unclear, however, if users take advantage of Touch ID technology and if they, indeed, employ stronger passcodes. In order to answer this question, at LERSSE, we conducted three user studies through which we found that users do not take an advantage of Touch ID and use weak unlocking secrets. Continue reading
Recently, Apple has introduced Touch ID, which allows a fingerprint-based authentication to be used for iPhone unlocking. It’s positioned to allow users to use stronger passcodes for locking their iOS devices, without substantially sacrificing usability. It is unclear, however, if users take advantage of Touch ID technology and if they, indeed, employ stronger passcodes. In order to answer this question, at LERSSE, we conducted three user studies through which we found that users do not take an advantage of Touch ID and use weak unlocking secrets. Continue reading
