Can real behavior of users, when it comes to security decisions, be observed in lab studies? A recent paper from my research group sheds light on this question.
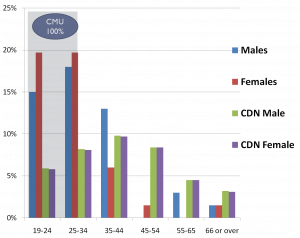
Initially, our goal was quite different. We replicated and extended a 2008 study conducted at CMU that investigated the e effectiveness of SSL warnings. To achieve better ecological validity, we adjusted the experimental design: allowing participants to use their web browser of choice and recruiting a more representative user sample.