
On May 11, 2018, with my UBC colleagues and PhD students, we have organized first full day event, where over 20 projects from UBC related to cybersecurity have been showcased. Over 170 attendees had come to UBC Cybersecurity Summit to see the projects. The summit also featured a keynote by CMU’s Professor Dr. Prof. Lujo Bauer and Gary Perkins, CISO for the Province of British Columbia. See more details on the summit web site. Stay tuned for Cybersecurity Summit 2020.
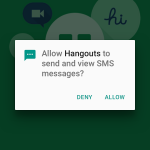
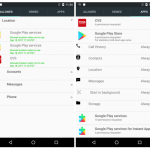 Modern mobile operating systems implement an ask-on-first-use policy to regulate applications’ access to private user data: the user is prompted to allow or deny access to a sensitive resource the first time an app attempts to use it. Prior research shows that this model may not adequately capture user privacy preferences because subsequent requests may occur under varying contexts. To address this shortcoming, LERSSE’s PhD student
Modern mobile operating systems implement an ask-on-first-use policy to regulate applications’ access to private user data: the user is prompted to allow or deny access to a sensitive resource the first time an app attempts to use it. Prior research shows that this model may not adequately capture user privacy preferences because subsequent requests may occur under varying contexts. To address this shortcoming, LERSSE’s PhD student 




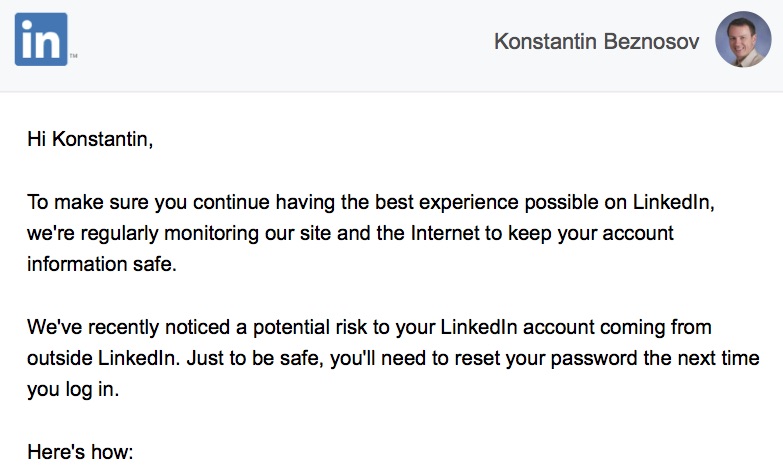
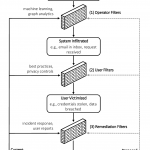 The orthodox paradigm to defend against automated social-engineering attacks in large-scale socio-technical systems is reactive and victim-agnostic. Defenses generally focus on identifying the attacks/attackers (e.g., phishing emails, social-bot infiltrations, malware offered for download). To change the status quo, we propose in
The orthodox paradigm to defend against automated social-engineering attacks in large-scale socio-technical systems is reactive and victim-agnostic. Defenses generally focus on identifying the attacks/attackers (e.g., phishing emails, social-bot infiltrations, malware offered for download). To change the status quo, we propose in 