As part of Innovate (in October) 2015, I gave a 7-minute “edutainment” talk, explaining in a very accessible form my current research, using an example of a recent study of iPhone’s TouchID:
As part of Innovate (in October) 2015, I gave a 7-minute “edutainment” talk, explaining in a very accessible form my current research, using an example of a recent study of iPhone’s TouchID:
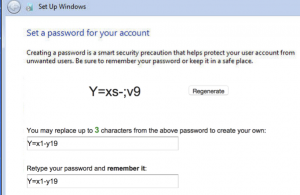 System-generated random passwords have maximum password security and are highly resistant to guessing attacks. However, few systems use such passwords because they are difficult to remember. In this paper, we propose a system-initiated user-replaceable password scheme called “Surpass” that lets users replace few characters in a random password to make it more memorable. Continue reading
System-generated random passwords have maximum password security and are highly resistant to guessing attacks. However, few systems use such passwords because they are difficult to remember. In this paper, we propose a system-initiated user-replaceable password scheme called “Surpass” that lets users replace few characters in a random password to make it more memorable. Continue reading
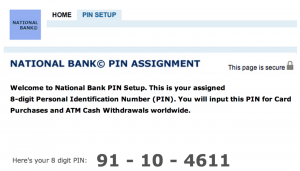 To ensure that users do not choose weak personal identification numbers (PINs), many banks give out system-generated random PINs. 4-digit is the most commonly used PIN length, but 6-digit system-generated PINs are also becoming popular. The increased security we get from using system-generated PINs, however, comes at the cost of memorability. And while banks are increasingly adopting system-generated PINs, the impact on memorability of such PINs has not been studied.
To ensure that users do not choose weak personal identification numbers (PINs), many banks give out system-generated random PINs. 4-digit is the most commonly used PIN length, but 6-digit system-generated PINs are also becoming popular. The increased security we get from using system-generated PINs, however, comes at the cost of memorability. And while banks are increasingly adopting system-generated PINs, the impact on memorability of such PINs has not been studied.
In a collaboration among Honeywell ACS Labs, Sungkyunkwan University, Oregon State University, University of Illinois at Urbana-Champaign, and UBC, we conducted a large-scale online user study with 9,114 participants to investigate the impact of increased PIN length on the memorability of PINs, and whether number chunking techniques (breaking a single number into multiple smaller numbers) can be applied to improve memorability for larger PIN lengths. Our findings have been reported at SOUPS ’15. Continue reading
 Recently, Apple has introduced Touch ID, which allows a fingerprint-based authentication to be used for iPhone unlocking. It’s positioned to allow users to use stronger passcodes for locking their iOS devices, without substantially sacrificing usability. It is unclear, however, if users take advantage of Touch ID technology and if they, indeed, employ stronger passcodes. In order to answer this question, at LERSSE, we conducted three user studies through which we found that users do not take an advantage of Touch ID and use weak unlocking secrets. Continue reading
Recently, Apple has introduced Touch ID, which allows a fingerprint-based authentication to be used for iPhone unlocking. It’s positioned to allow users to use stronger passcodes for locking their iOS devices, without substantially sacrificing usability. It is unclear, however, if users take advantage of Touch ID technology and if they, indeed, employ stronger passcodes. In order to answer this question, at LERSSE, we conducted three user studies through which we found that users do not take an advantage of Touch ID and use weak unlocking secrets. Continue reading
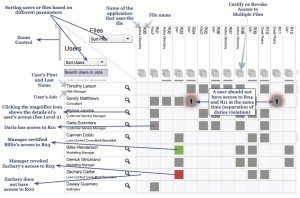 Research led by LERSSE Ph.D. student Pooya Jaferian will be featured at SOUPS this July. By interviewing IT professionals, he has explored access review activity in organizations, and then modeled access review in the activity theory framework. The model suggests that access review requires an understanding of the activity context including information about the users, their job, their access rights, and the history of access policy. Guidelines of the activity theory were used to design a new user interface, AuthzMap, which was compared to two state of the practice. The experiments demonstrated that AuthzMap improved the efficiency of access review most scenarios. Read the full paper for details.
Research led by LERSSE Ph.D. student Pooya Jaferian will be featured at SOUPS this July. By interviewing IT professionals, he has explored access review activity in organizations, and then modeled access review in the activity theory framework. The model suggests that access review requires an understanding of the activity context including information about the users, their job, their access rights, and the history of access policy. Guidelines of the activity theory were used to design a new user interface, AuthzMap, which was compared to two state of the practice. The experiments demonstrated that AuthzMap improved the efficiency of access review most scenarios. Read the full paper for details.
 My Ph.D. student San-Tsai Sun has successfully defended and submitted the final version of his thesis “Towards Improving the Usability and Security of Web Single Sign-On Systems.” He’s moving back to industry, where he will be applying his expertise in web security to real-world systems. Congratulations to San-Tsai on very successful completion of the Ph.D. program, with many quality publications.
My Ph.D. student San-Tsai Sun has successfully defended and submitted the final version of his thesis “Towards Improving the Usability and Security of Web Single Sign-On Systems.” He’s moving back to industry, where he will be applying his expertise in web security to real-world systems. Congratulations to San-Tsai on very successful completion of the Ph.D. program, with many quality publications.
My department has made a short introductory video-clip about my research group LERSSE. For those who won’t read papers but still want to get an idea about what kind of research my graduate students do, just sit back and enjoy this 3-minute long summary.
httpv://www.youtube.com/watch?v=mJMxjnwfe8U
Students in my graduate course on computer security are presenting their term papers on April 10. The topics vary from evaluation of Sybil detection mechanisms to detection of DDoS attacks on grid clusters. This mini-conference is open to public.
Password meters tell users whether their passwords are “weak” or “strong.” In this paper, we report on a laboratory experiment to examine whether these meters influenced users’ password selections when they were forced to change their real passwords, and when they were not told that their passwords were the subject of a study. We observed that the presence of meters yielded significantly stronger passwords. We then performed a followup field experiment to test a different scenario: creating a password for an unimportant account. In this scenario, we found that the meters made no observable difference: participants simply reused weak passwords that they used to protect similar low-risk accounts. We conclude that meters result in stronger passwords when users are forced to change existing passwords on “important” accounts and that individual meter design decisions likely have a marginal impact.
More details are in the paper, which will be presented at CHI ’13 held April 27-May 3.
OpenID is an open and promising Web single sign-on (SSO) solution. The research led by my Ph.D. student San-Tsai Sun investigates the challenges and concerns web users face when using OpenID for authentication, and identifies what changes in the login flow could improve the users’ experience and adoption incentives. Continue reading